Difference between revisions of "ZMNinja"
| (6 intermediate revisions by the same user not shown) | |||
| Line 99: | Line 99: | ||
to block certain ports, or all ports depending... That will not be covered in this guide at the moment. | to block certain ports, or all ports depending... That will not be covered in this guide at the moment. | ||
In /etc/fail2ban/jail.conf (at the end) (or jail.local to avoid updates overwriting) | In /etc/fail2ban/jail.conf (at the end) (or jail.local/jail.d to avoid updates overwriting) | ||
[zoneminder] | [zoneminder] | ||
# Zoneminder HTTP/HTTPS web interface auth | # Zoneminder HTTP/HTTPS web interface auth | ||
| Line 106: | Line 106: | ||
port = http,https | port = http,https | ||
logpath = /var/log/zm/web_php.log* | logpath = /var/log/zm/web_php.log* | ||
| Line 140: | Line 139: | ||
fail2ban-regex /var/log/zm/web_php.log zoneminder.conf | fail2ban-regex /var/log/zm/web_php.log zoneminder.conf | ||
fail2ban-client status zoneminder | fail2ban-client status zoneminder | ||
fail2ban-client unban <ipaddress> | |||
and | and | ||
tail -F /var/log/zm/web_php.log | tail -F /var/log/zm/web_php.log | ||
It should ban after 5 tries with zminja (which does two logins each time you try to save settings). | It should ban after 5 tries with zminja (which does two logins each time you try to save settings). It will block on either a correct user with incorrect pass, or a non existent user with an incorrect pass. | ||
====Additional Steps==== | |||
* Increase bantime from 10m to something higher (1440m), | |||
* set the block action to nftables-allports (since iptables is no longer in debian but fail2ban has fail2update). These are in jail.conf. | |||
* https://www.the-art-of-web.com/system/fail2ban-howto/ | * https://www.the-art-of-web.com/system/fail2ban-howto/ | ||
Latest revision as of 10:19, 29 October 2024
ZMNinja is a frontend for mobile phones and x86 computers.
This is the community wiki documentation on ZMNinja. Please refer to the official docs for more information. https://zmninja.readthedocs.io
Setting up ZMNinja - serverside
Typically when setting up ZMNinja you will be doing so for WAN access. This will require the following:
- Confirm API is working (see API)
- Enable SSL for apache (covered briefly in API page above)
- Make sure php-gd is installed (picture thumbnails)(apt-get install php-gd, then restart apache)
- MySQL: update zm.Config set Value = 1 where Name = "ZM_AUTH_HASH_LOGINS"; (picture thumbnails)
There isn't much more to it than that. If your API is working, and you have SSL working, then ZMNinja should do its job. Picture thumbnails will work if you enable auth hash logins and have gd support in php.
This assumes you have installed ZM properly. The easiest (and most maintained) guides are Debian, and Ubuntu.
Setting up ZMNinja - client
The next step is to download ZMNinja Pro from your app store (or if using a desktop, the x86 binary from the releases of the git repo),
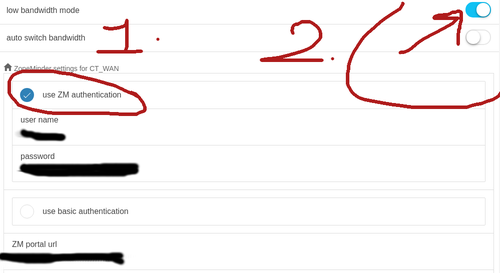
- Enable ZM Authentication
- Enable Low bandwidth mode
- Add username and password (this will only be typed once, then ZMNinja will save it.)
- Type in the IP address into the 3 paths
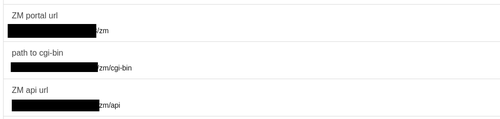
The rest of ZMNinja can be left at defaults. The paths can look something like this (Note that usually it autofills partway for you, once you type in the IP):
ZM Portal URL: https://WANIPOFSERVER/zm/ path to cgi-bin: https://WANIPOFSERVER/zm/cgi-bin ZM api url: https://WANIPOFSERVER/zm/api
Security
It is recommended to have strong passwords for ZMNinja on the WAN. One method to isolate your network from a potentially vulnerable Zoneminder system on the WAN is to have a separate static IP for your camera network, and then have all of your office LAN use ZMNinja out to the WAN and back to view cameras.
See also: https://wiki.zoneminder.com/Ubuntu_Install_ZoneMinder_on_Ubuntu_Server#Hardening_Webserver
SSL should be the only port accessible via WAN. SSL certificates should be setup.
Geoblocking
Geoblocking is a good idea. There are guides online for geoblocking such as:
e.g.
#apt-get install libapache2-mod-geoip #a2enmod geoip
geoip.conf
<IfModule mod_geoip.c> GeoIPEnable On GeoIPDBFile /usr/share/GeoIP/GeoIP.dat #NOTE: ipv6 requires another file, see /usr/share/GeoIP. </IfModule>
Now, edit your /etc/apache2/conf-available/zoneminder.conf to look something like this:
Alias /zm /usr/share/zoneminder/www
<Directory /usr/share/zoneminder/www>
Options -Indexes +FollowSymLinks
<IfModule mod_dir.c>
DirectoryIndex index.php
</IfModule>
AllowOverride FileInfo Options
SetEnvIf GEOIP_COUNTRY_CODE FR AllowCountry
Deny from all
Allow from env=AllowCountry
</Directory>
php test script (note: remove html comment tags)
<!--?php $country_name = apache_note("GEOIP_COUNTRY_NAME"); echo "Land: " . $country_name; ?-->
Note that more configuration on zoneminder.conf will be needed, but the above should at least show you that it's working. Beware that existing connections may need to time out if one is open. The expected result is a 403 (access forbidden) error. Verify the error in access.log.
Fail2ban
This guide is relevant for 1.36.31. If you have an older version, please refer to the forums. There are 3 steps to this.
- Fix the date time.
- Configure failban config files
- Test the setup.
Fix Datetime
First fix the datetime... [1]
Starting with 1.36.20 the above Regex will no longer work due to the DATETIME_FORMAT_PATTERN including time zone information and not following the previous pattern as used by ZM To resolve this enter the following into the Options / System / DATETIME_FORMAT_PATTERN yyyy/MM/dd HH:mm:ss
Configure jail.d/zoneminder.conf and filter.d/zoneminder.conf
There are two parts to fail2ban that are required for a jail. jail.conf enables the jail, along with some settings, and filter.d/zoneminder.conf contains the filter/regex. Note that there is also additional configuration that may or may not be required. The actions.d folder for example has the option to block certain ports, or all ports depending... That will not be covered in this guide at the moment.
In /etc/fail2ban/jail.conf (at the end) (or jail.local/jail.d to avoid updates overwriting)
[zoneminder] # Zoneminder HTTP/HTTPS web interface auth # Logs auth failures from /var/log/zm/web_php.log error log enabled = true port = http,https logpath = /var/log/zm/web_php.log*
In /etc/fail2ban/filter.d/zoneminder.conf should read:
[INCLUDES] before = apache-common.conf [Definition] # pattern: [Wed Apr 27 23:12:07.736196 2016] [:error] [pid 2460] [client 10.1.1.1:47296] WAR [Login denied for user "test"], referer: #https://zoneminderurl/i$ # # # Option: failregex # Notes.: regex to match the password failure messages in the logfile. #failregex = ^%(_apache_error_client)s WAR \[Login denied for user "[^"]*"\] #ignoreregex = filter = failregex = ^\s*web_php\[\d+\]\.ERR \[<HOST>\].*includes/auth.php* # Notes: # Tested on Zoneminder 1.29.0 # # Author: John Marzella
This is based on the existing Debian Buster zoneminder.conf. Notice that I've commented out the obsolete regex and added the viable one for 1.36. And, yes the filter clause should be empty.
Test That it Works
Confirm it works with
fail2ban-regex /var/log/zm/web_php.log zoneminder.conf fail2ban-client status zoneminder fail2ban-client unban <ipaddress> and tail -F /var/log/zm/web_php.log
It should ban after 5 tries with zminja (which does two logins each time you try to save settings). It will block on either a correct user with incorrect pass, or a non existent user with an incorrect pass.
Additional Steps
- Increase bantime from 10m to something higher (1440m),
- set the block action to nftables-allports (since iptables is no longer in debian but fail2ban has fail2update). These are in jail.conf.
- https://www.the-art-of-web.com/system/fail2ban-howto/
- https://fail2ban.readthedocs.io/en/latest/filters.html
Troubleshooting
If you have trouble, refer to the Debug Logs included in ZMNinja. ZMNinja also has extensive docs.
For further information, refer to the official docs.